DC610 - Pub Crawl CTF
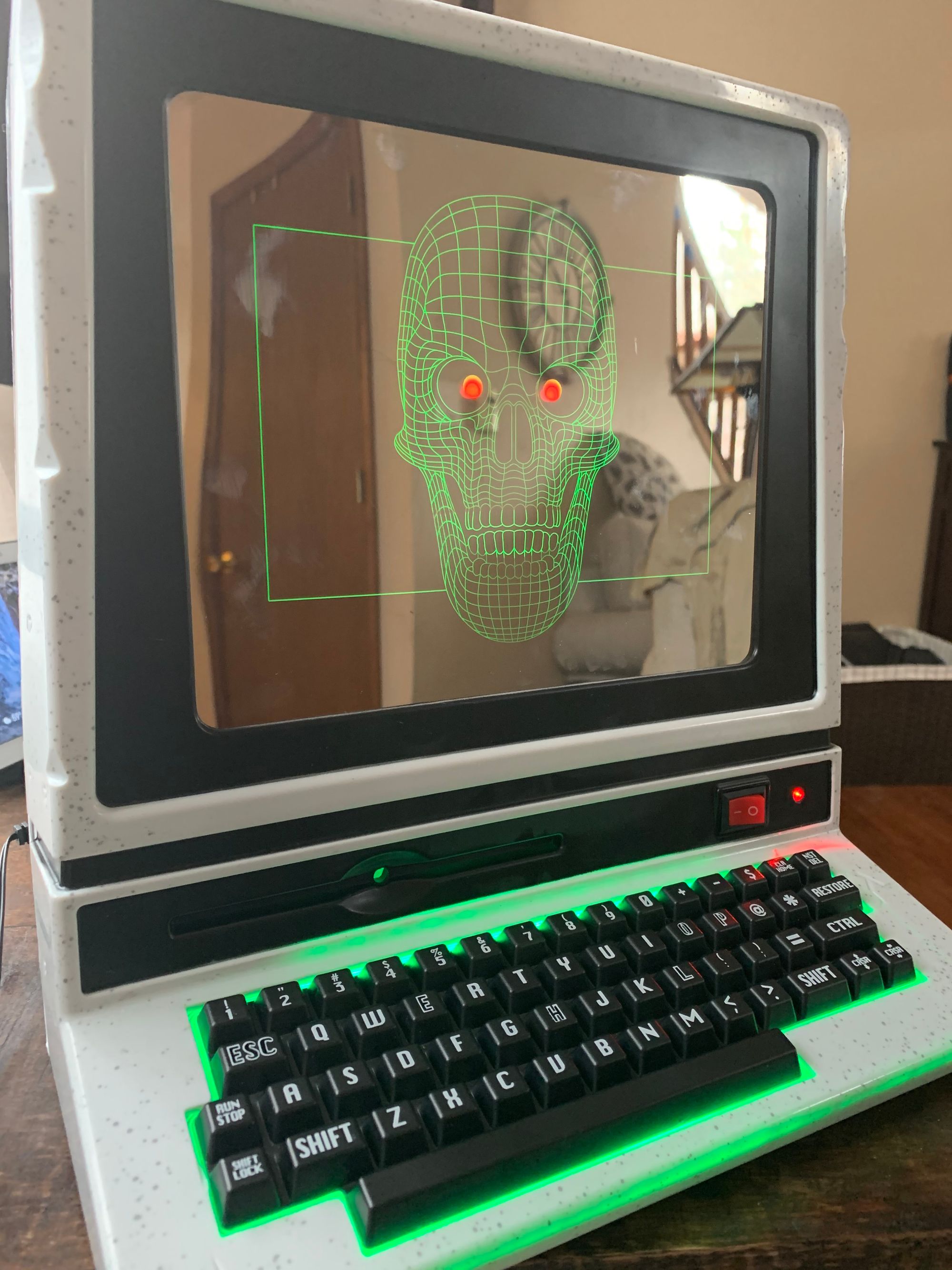 That MS-DOS feel with the rocker switch!
That MS-DOS feel with the rocker switch!
Introduction
Doing DEFCON stuff doesn’t have to end with the closing ceremonies in Vegas. You can have DEFCON fun all year round by joining and hanging out with a local DEFCON group - which is what I did! After being introduced to my local group, I learned that they would be having an upcoming CTF that was to be setup in a pub crawl fashion along Northampton Street in downtown Easton, PA. I was quick to volunteer to create a few flags to help add to DC610’s first CTF, and this post details my journey into that.
High-level: CTF’s were placed at five different pubs up and down the street where participants could wander in, sit down and have some food or drink, and connect to a local RPi to engage in some CTF fun.
The CTF I created was Doom themed for the 25th anniversary of Doom (albeit the unexpected delay of Doom Eternal), named Cyb3rda3m0n. Get it? Demon/Daemon? Har, har. It was built on a Raspberry Pi using the following:
- Docker - containerize the CTF server
- hostapd - give out some WiFi to connect to the CTF server
- Some inotify scripts forked from @Gangifs GitHub repository for flag generation
This was the first CTF I’ve ever built, so I’m not 100% pleased with myself but we anticipate future CTF’s with DC610 so there’s always room for a Version 2!
That case, though!
Initially, I was looking to put the RPi into an old (and broken) Nintendo 64 shell and use an OLED into a hollowed out cartridge to look like the Doom 64 cartridge (yeah, that got delayed too) but ended finding this gem at Target.
I figured, all things considered, this was an awesome choice. I ended up cracking it open, and cutting out a notch in the back to mount the RPi in using some velcro tape.
The biggest thing I regret for this CTF was the lack of a small LCD screen. I wish I had more time to purchase an LCD, mount it, and write something to interact with the CTF, like: Doom Guy looking around while idle, Doom Guy killing an Imp when a flag is found, and displaying the SSID and URL to the CTF. Like I said, there’s always Version 2. All rights reserved, don’t steal, legal stuff.
The CTF - Cyb3rda3m0n
The CTF server itself was running as a Docker container with some volumes mapped to the host OS so I could have an easier time using a modified version of @Gangrif inotify scripts to watch for file access events against the “flag” files - which I also setup as a cron job so when the RPi was powered on, the inotify scripts would start after the Docker container launched so everything was plug and play.
The Docker container itself was running Ubuntu Server with Apache, PHP, and some other Apache-related modules.
The content of the CTF was rather simple being some basic HTML and PHP for login fields and system() functions… that were able to take some input from the user. It’s a CTF, after all.
There were three flags in total, below is a high-level of what they were about:
- d00mguy - the participant would start by enumerating
robots.txtand head for the first directory which was an open index. There were three subfolders, two of which contained a Zombie Marine and an Imp as decoys. The other subfolder simply called a flag and presented it to the participant - mast3rm1nd - the participant would go to the second directory found in robots.txt and would be faced with a UAC login page. The source of the webpage had the username and password (doomguy/noimps) as a comment in the HTML to which you login and receive the flag.
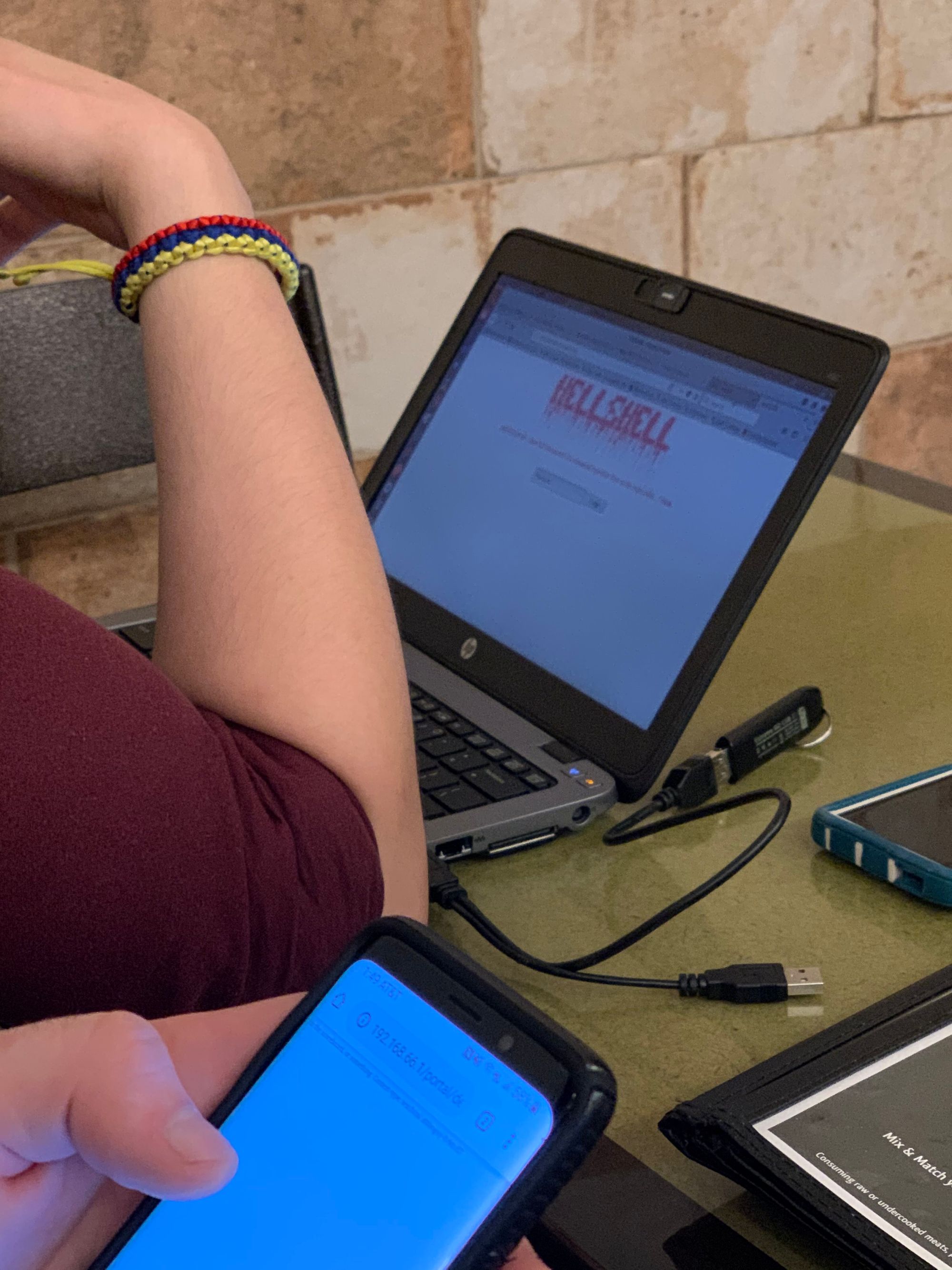
- cyb3rda3m0n - the final directory found in robots.txt would bring you to a taunting message from the Cyb3rDa3m0n himself, and encourage you to follow a link to their PHP shell. The PHP shell, H3llSh3ll, is a password protected shell. A clue on-screen is that the developer is pretty sure he fixed the Revenant’s command injection flaw. If the participant attempts to pipe in some Unix commands, they can look around the working directory, and grep the flag
Also, my PHP shell was “weaponized” by a participant. They used it to find all the other flags! iaintevenmad.jpg - if anything they should have been awarded more points for innovation!
Again, it was simple and had the mindset of what was originally proposed by DC610, being it should be simple enough to do on a smartphone given it’s essentially a pub crawl still. Given the turn out, and nearly everyone whipping out their laptops (and other CTF’s being really challenging) there’s room for improvement for the next DC610 CTF event!
Conclusion
As always, the retrospective. Here’s what I’m looking forward to making Cyb3rDa3m0n v2
- More challenging!
- Include an LCD screen in the case for added effect and function
- Real world CVE’s